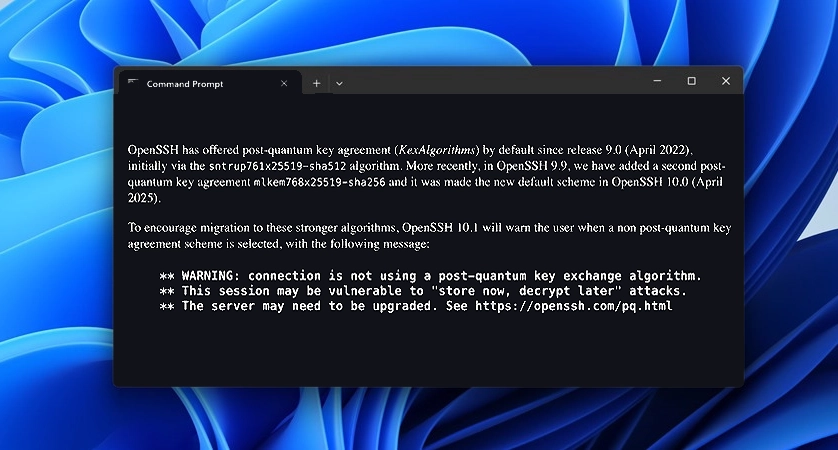
WARNING: connection is not using a post-quantum key exchange algorithm.
Most people imagine cyberattacks as something loud and immediate: a hacker breaking into a system, stealing files, or locking everything down with ransomware. But the next major cybersecurity threat may not look like an attack at all. It could be happening quietly, right now, as encrypted data moves across the internet—captured, stored, and waiting for the moment when future technology makes it easy to read.
The Quiet Cyber Threat Already Happening: Store Now, Decrypt Later
Across the internet today, enormous volumes of encrypted traffic are being captured and stored. While this data appears harmless because modern encryption protects it, that protection depends on the limits of current computing power. If large-scale quantum computers become practical, the encryption guarding those archives could be broken, turning years of stored network traffic into readable information.
In that moment, everything captured today could effectively become tomorrow’s plaintext. Many systems—including older SSH deployments and infrastructure that has not adopted post-quantum protections—still rely entirely on classical cryptography. Until those systems transition to quantum-resistant methods, the data they transmit may remain exposed to the long-term risk of future decryption.
What the Warning Actually Means
The warning shown in the terminal comes from OpenSSH, a widely used tool for secure remote access. It indicates that the connection being established is not using a post-quantum key exchange algorithm. In simple terms, the encryption protecting the session relies on traditional cryptography designed long before quantum computers were considered a realistic threat.
For decades, internet security has depended on systems such as RSA and elliptic-curve cryptography. These methods protect server logins, financial transactions, private communications, and critical infrastructure by relying on mathematical problems that are extremely difficult for classical computers to solve. With current computing power, breaking these encryption systems would take millions of years.
The warning highlights that this protection still relies entirely on those classical assumptions. While these algorithms remain secure against traditional computers, sufficiently powerful quantum computers could potentially break them using advanced algorithms such as Shor’s algorithm.
This concern is often described as “store now, decrypt later.” Attackers can capture encrypted internet traffic today and store it, even if they cannot decrypt it yet. Instead of breaking the encryption immediately, they archive the data and wait for future computing advances that may make decryption possible.
That means the risk is not limited to future communications. Data transmitted today—emails, server credentials, financial records, internal documents, and private messages—could already be collected and stored. When quantum computing matures, that archived data could potentially be decrypted.
This is why the warning exists. It serves as a signal that the encryption protecting the connection has not yet been upgraded for the coming era of quantum computing.
In response, the cybersecurity community is developing post-quantum cryptography—new encryption methods designed to resist attacks from both classical and quantum computers. As these technologies are adopted across infrastructure, cloud systems, and security tools, they will help ensure that data captured today remains secure in the future.
Until that transition is widespread, many encrypted connections will continue relying on algorithms that were never designed to withstand quantum-level computing power. The warning is simply a reminder that the shift to quantum-safe security is already underway.
Why Quantum Computing Threatens Modern Encryption
Modern cryptographic systems such as RSA cryptosystem and Elliptic Curve Cryptography derive their security from mathematical problems that are considered computationally infeasible for classical computers to solve within a reasonable timeframe. These systems underpin a vast portion of modern digital security infrastructure, protecting everything from secure web browsing and encrypted messaging to financial transactions and remote server access.
At the core of these cryptographic schemes lies a principle known as computational hardness. Encryption algorithms are designed so that certain mathematical operations are easy to perform in one direction but extremely difficult to reverse without special information, typically a private key. In the case of RSA, the security of the system depends on the difficulty of factoring extremely large composite numbers into their prime components. For sufficiently large numbers—often hundreds or thousands of bits long—no efficient classical algorithm currently exists that can perform this factorization within practical time limits.
Similarly, elliptic-curve cryptography relies on the computational difficulty of the elliptic curve discrete logarithm problem. Given two points on an elliptic curve, determining the scalar multiplier that connects them is believed to require enormous computational effort using classical methods. These problems form the foundation of widely deployed protocols used in secure communication systems such as TLS, SSH, and many authentication frameworks.
Under classical computational models, these cryptographic problems are considered secure because the resources required to solve them grow exponentially as the key size increases. Even with massive distributed computing power, breaking modern encryption keys by brute force or classical mathematical attacks would take an astronomical amount of time—often estimated in millions or billions of years. This computational barrier has historically provided confidence that encrypted data would remain confidential for the foreseeable future.
Quantum computing, however, introduces a fundamentally different computational paradigm. Instead of processing information using classical bits, which exist strictly in one of two states—0 or 1—quantum computers operate using quantum bits, or qubits. A qubit can exist in a superposition of states, meaning it can represent both 0 and 1 simultaneously until measured. When multiple qubits interact through quantum entanglement, they form complex probabilistic systems that allow certain computations to be performed in ways that have no classical equivalent.
This property enables quantum computers to explore extremely large solution spaces more efficiently than classical machines. While a classical computer evaluates possible solutions sequentially or through limited parallelism, a quantum computer can manipulate probability amplitudes across many states simultaneously, enabling entirely new classes of algorithms.
One of the most significant breakthroughs in quantum algorithms is Shor’s Algorithm, developed by mathematician Peter Shor in 1994. Shor’s algorithm demonstrates that a sufficiently powerful quantum computer could factor large integers and compute discrete logarithms in polynomial time, a dramatic improvement over the best-known classical algorithms. Problems that would otherwise require astronomical computational effort suddenly become tractable once quantum computational resources reach the required scale.
The implications for cryptography are profound. Because RSA and elliptic-curve cryptography rely on the difficulty of factoring and discrete logarithm problems, the existence of large-scale quantum computers capable of running Shor’s algorithm would effectively undermine the mathematical assumptions that make these systems secure. Encryption schemes that have protected digital communications for decades could potentially be broken in a matter of hours or days rather than millions of years.
This possibility has led researchers to recognize that many widely deployed cryptographic systems are not inherently quantum-resistant. While current quantum hardware remains limited in scale and stability, steady advances in quantum engineering suggest that more powerful quantum processors will eventually emerge. Once a quantum computer with sufficient qubits, error correction, and coherence time becomes operational, it could render large portions of the current public-key cryptographic infrastructure obsolete.
As a result, the global cryptographic community has begun developing and standardizing post-quantum cryptographic algorithms designed to resist both classical and quantum attacks. These systems rely on alternative mathematical structures, such as lattice-based cryptography, hash-based signatures, and code-based encryption schemes, which are believed to remain secure even in the presence of quantum computational capabilities.
The transition to quantum-resistant cryptography is now considered one of the most significant upcoming shifts in cybersecurity. While the precise timeline for large-scale quantum computers remains uncertain, the potential impact on modern encryption systems is clear: once quantum computation reaches the necessary threshold, many of today’s most trusted cryptographic protections could become vulnerable almost immediately.
The Danger of Session Capture
Encrypted connections such as SSH and HTTPS are designed to protect information while it moves across the internet. They secure login sessions, financial transactions, database communication, and countless other interactions that businesses depend on every day. Yet attackers do not always need to break that encryption immediately. Instead, they can quietly capture encrypted traffic and store it for future analysis, preserving entire sessions of network activity without ever triggering a security alert.
Within those stored records may be passwords, financial activity, private messages, API keys, authentication tokens, backups, database exchanges, and other sensitive business information. Although the data may remain unreadable today, advances in computing—particularly quantum computing—could eventually make it possible to decrypt those archived sessions. The danger is not limited to future communication. The real exposure lies in the possibility that information being transmitted securely today could become readable years later once the technology to unlock it finally arrives.
Why This Matters to Businesses
Modern businesses depend on encrypted connections for nearly every critical operation. Remote server administration, cloud infrastructure access, database replication, payment processing, customer data protection, software deployments, and backups all move through encrypted channels every second of the day. Encryption creates the sense that this activity is safely sealed from outside eyes, allowing organizations to operate with confidence. Yet the protection most companies rely on assumes that the encryption protecting those sessions will remain difficult to break indefinitely. When that assumption changes, the security of everything transmitted through those channels changes with it.
If attackers capture encrypted sessions today, they do not need immediate access to the contents. They can simply store the traffic and wait. Inside those stored packets could be financial records, customer identities, internal architecture maps, authentication tokens, API keys, and trade secrets that define the competitive edge of a business. In a quantum-enabled future, an attacker may never need to breach a server, guess a password, or trigger an alert. They only need to unlock the archive of traffic they already collected. At that moment, years of protected communication can quietly become visible all at once.
Post-Quantum Cryptography: The Defense
Post-quantum cryptography is emerging as the next line of defense against the long-term risks posed by quantum computing. These cryptographic systems are designed specifically to withstand attacks from both classical computers and the powerful algorithms expected to run on future quantum machines. In practical terms, this means developing encryption methods that remain secure even if the mathematical shortcuts used by quantum algorithms dramatically reduce the time required to break traditional encryption systems like RSA or elliptic-curve cryptography.
Modern security tools are already beginning this transition. Recent versions of OpenSSH support hybrid key-exchange mechanisms such as ML-KEM combined with X25519 or SNTRUP combined with X25519. These systems intentionally blend classical cryptography with quantum-resistant algorithms, creating layered protection so that even if one method becomes vulnerable, the connection remains secure. Security researchers increasingly advise organizations to begin adopting post-quantum capable encryption now, well before large-scale quantum computers become practical, ensuring that the data transmitted today cannot become tomorrow’s exposed archive.
The Migration Window Is Closing
For decades, organizations treated security upgrades as a reaction to immediate threats. Systems were patched when vulnerabilities were discovered, and encryption standards were updated only after weaknesses became practical to exploit. That reactive strategy worked when attackers needed to break defenses in real time. The emerging quantum threat changes that model entirely. The timeline of risk is no longer tied to when an attack happens, but to when the captured data finally becomes decryptable.
Today, attackers can quietly collect encrypted network traffic and store it indefinitely. Years later, when sufficiently powerful quantum computers emerge, that archived data can be decrypted and examined in full. What once appeared secure could suddenly reveal financial records, internal communications, system credentials, and sensitive intellectual property. In this new reality, the real breach may have already occurred. If the encryption protecting your data today is not quantum-safe, the information may already be sitting in someone’s archive, simply waiting for the moment it can be unlocked.
Why Acting Now Matters
Quantum security carries a unique challenge that most cybersecurity threats do not. Once encrypted communication is transmitted across a network, it cannot be taken back or protected retroactively. If an attacker captures that traffic, it can be stored indefinitely, waiting for the day when the encryption protecting it becomes easier to break. In other words, the exposure risk begins the moment the data is sent, not when the encryption is eventually cracked.
Every day that systems continue operating without quantum-resistant encryption adds more potentially vulnerable data to the historical record. Financial transactions, internal communications, authentication exchanges, and system architecture details quietly accumulate in encrypted form across network logs and archives. Organizations that begin adopting quantum-safe protections now dramatically reduce the amount of data that could later be decrypted. Those that delay may unknowingly build a long-term archive of sensitive information that future technology could suddenly unlock.
A Simple Step Toward Quantum Resilience
Upgrading infrastructure to support post-quantum encryption is not simply a matter of compliance or guarding against a distant theoretical threat. It is about preserving the long-term confidentiality of the information being transmitted today. Every encrypted login, financial transaction, customer interaction, and system exchange adds to a growing archive of protected communication. The strength of that protection depends on the assumption that current cryptographic systems will remain difficult to break. As that assumption begins to shift, the value of preparing early becomes clear.
Even if practical quantum computers are still years away, the data being transmitted right now will still exist when those systems arrive. That reality is why the transition to quantum-safe encryption has already begun across major cloud platforms, financial institutions, government agencies, and critical infrastructure providers. Security leaders increasingly view early adoption not as a luxury, but as the emerging baseline for responsible data protection. Organizations that move first ensure that the information flowing through their systems today remains confidential far into the future.
The Bottom Line
Encryption has protected the internet for decades, forming the foundation of secure communication, online commerce, and modern cloud infrastructure. But the arrival of the quantum era is expected to change the assumptions those systems were built on. The encryption that protects data today may not remain secure forever, especially as new computational capabilities begin to challenge the mathematical problems that traditional cryptography relies upon.
Every encrypted connection made today could be quietly stored somewhere, preserved in massive data archives waiting for the moment when decryption becomes far easier. The most effective defense is not to wait for that moment, but to upgrade encryption systems before it arrives. In the quantum future, the critical question will not simply be whether your data was encrypted. The real question will be whether it was encrypted using methods designed to remain secure in a quantum-capable world.
Act Now! Before Your Data Becomes Tomorrow’s Plaintext
If your servers, websites, or infrastructure are still running traditional encryption stacks, now is the time to evaluate whether they are prepared for the coming quantum era. Upgrading SSH implementations, modernizing encryption protocols, and adopting post-quantum capable cryptography can significantly reduce long-term security risk. Businesses that prepare now protect the confidentiality of the data they transmit today, while those that delay may discover that trusted encrypted archives have quietly become readable.
Host Much helps organizations modernize their infrastructure, hosting environments, and server security with hardened deployments and post-quantum ready encryption. To see whether your systems are prepared for the quantum future, visit HostMuch.com and schedule a consultation for a full infrastructure security review.
Web Design
Answers to your
 Questions .
Questions .
Our team is ready to answer your questions.
